I have been deliberating since my last post as to what this post should consist of. I knew I wanted to do some domain and technology footprinting, but there is so much extra stuff that can be included in the post. I have decided to limit the scope, therefore not including the extras(these posts will come later).
Information gathering
There is an abundance of web services that can be used to enumerate all sorts of information about anything on the web. For this post, I have specifically chosen to focus on what information can be enumerated from websites. Knowing information about the domain and technologies used for the website, can help you determine where the website is vulnerable.
To begin with, we have a website called Builtwith. Builtwith will scan the website headers, looking for clues as to what technologies are used. The standard results will include the web server type, CSS and html version. The more variable results will have information about any CMS systems used, frameworks, databases etc.
To use Builtwith, you enter a web address in the search field, and click on “Lookup”.

Builtwith will scan the website, and return its findings as follows:
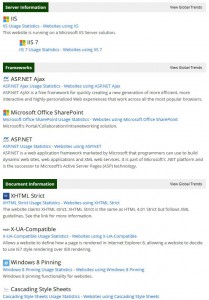
As you can see, we have already started building a picture in our minds as to how the website is put together. A little further digging and you will know what versions are being used. We can then search for vulnerabilities associated with those technologies. Try it out with a few of your favourite websites.
Netcraft
A second website that returns similar information, is Netcraft. Netcraft tends to miss some of the stuff that Builtwith returns, however it includes in its results some things that Builtwith does not.

For example, information about the network and hosting. As can be seen here:

Domain registration details
Lastly, we may want some information about domain registration. There are a few websites that can give you this information, most of which are domain specific. Eg. Some will only be able to provide information from the .com domain, while others will be specific to a country. The website will perform a whois on the domain, and return the results. The kind of information you can expect to find will be billing history, names of people who registered the domain(sometimes helpful, it could be someone working in the company), their contact details, physical address of the person/company etc.
A commonly used tool is the whois function on InterNIC. InterNIC can provide whois information for the following domains: .aero, .arpa, .asia, .biz, .cat, .com, .coop, .edu, .info, .int, .jobs, .mobi, .museum, .name, .net, .org, .pro, or .travel.
For co.za, you can use the whois function on co.za.
On the face of it, not much can be done with all of this information. However, in the reconnaisance phase of an attack, any information is good information. The more you have, the more you can use to infer useful plans of attack.